Understanding the Concept of Need Admitted Penthouse Encryption Complexity
In the realm of cryptography, encryption methods continue to evolve to cope with the increasing demands of security and complexity. As we delve into the world of encryption, it's essential to comprehend the intricacies involved in securing data. The term "need admitted penthouse encryption complexity" might seem perplexing at first glance, but it's actually a reference to the advanced encryption techniques employed by modern cryptographic systems.Key Wrapping and Symmetric Keys
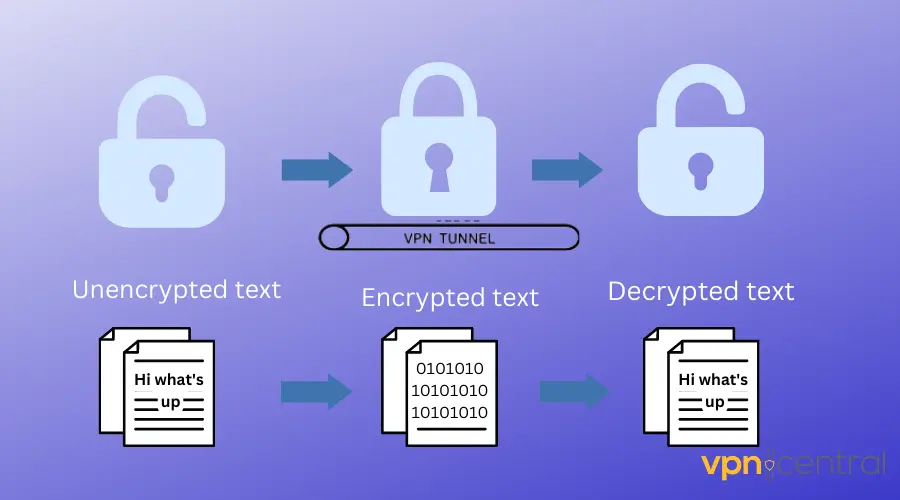
Key wrapping is a method used to encrypt symmetric keys with another symmetric key, known as a key wrapping key, to provide integrity protection. This is crucial in securing sensitive data, like symmetric keys, to prevent unauthorized access. Symmetric keys, such as those used in Triple-DES and AES algorithms, are powerful tools for encryption, but they require robust protection methods to prevent key exposure.Nov 17, 2025 - Encryption and decryption can be seen as components of the coding and decoding subsystems in a classic communication mechanism. However, we need to consider an additional layer of security.
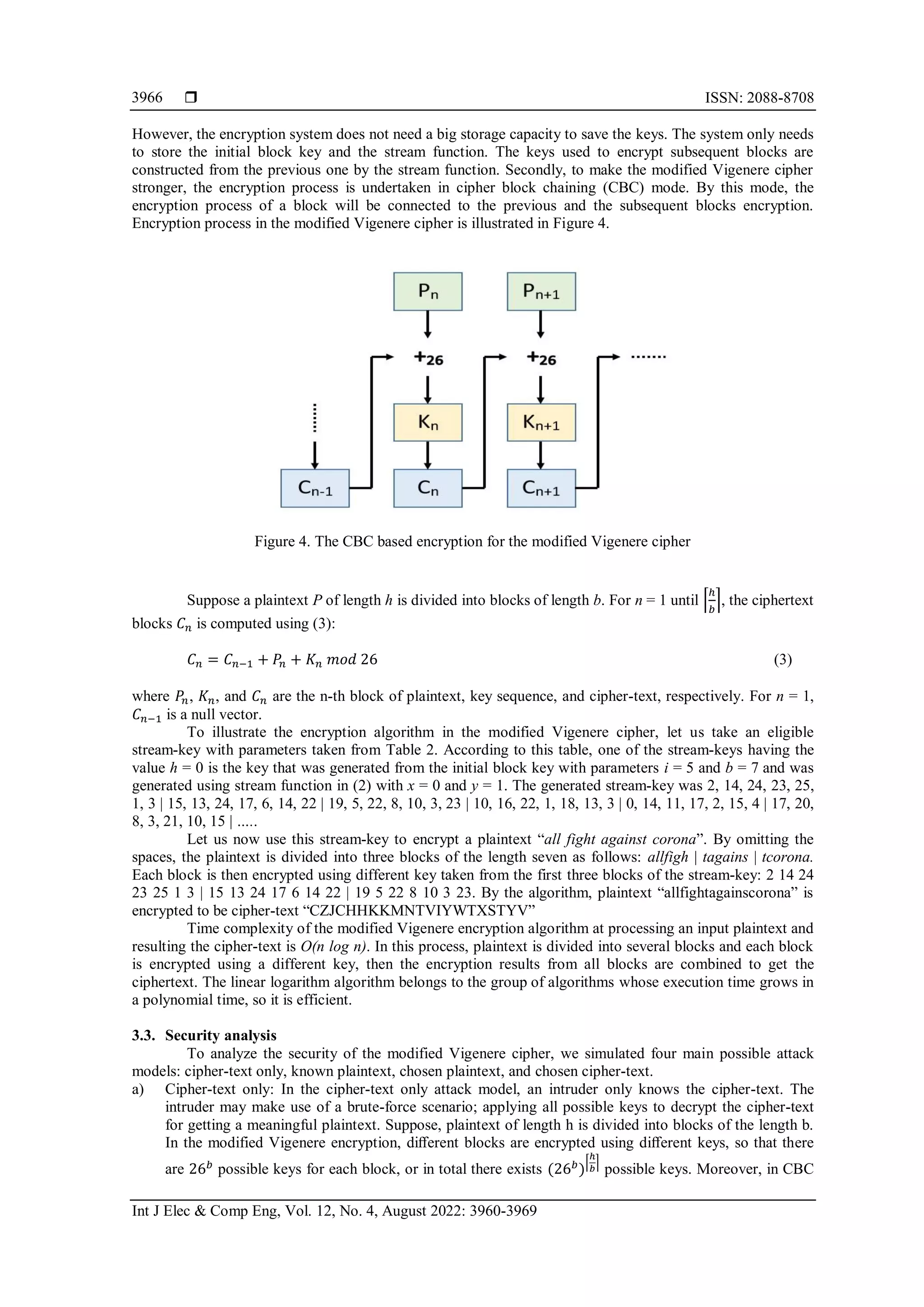
Quantifying Time Complexity in Encryption

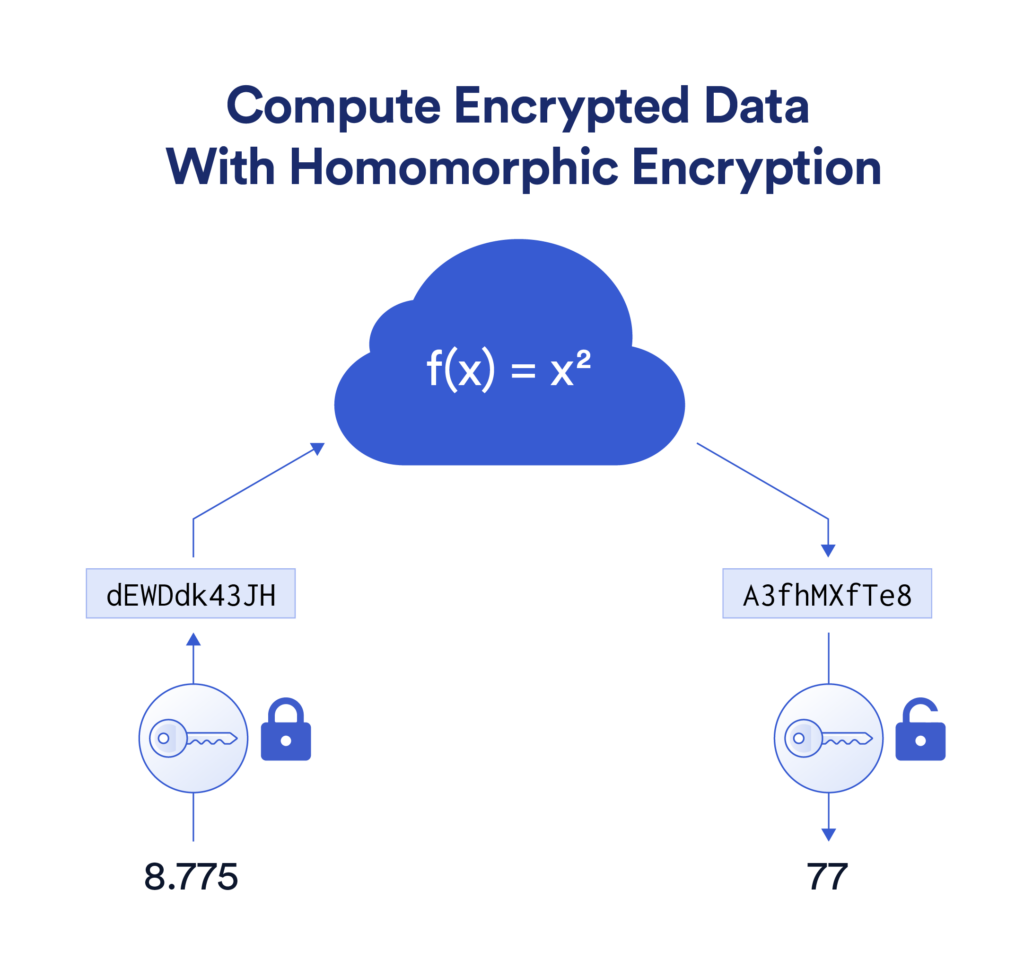
The Intersection of Computational Complexity and Homomorphic Encryption
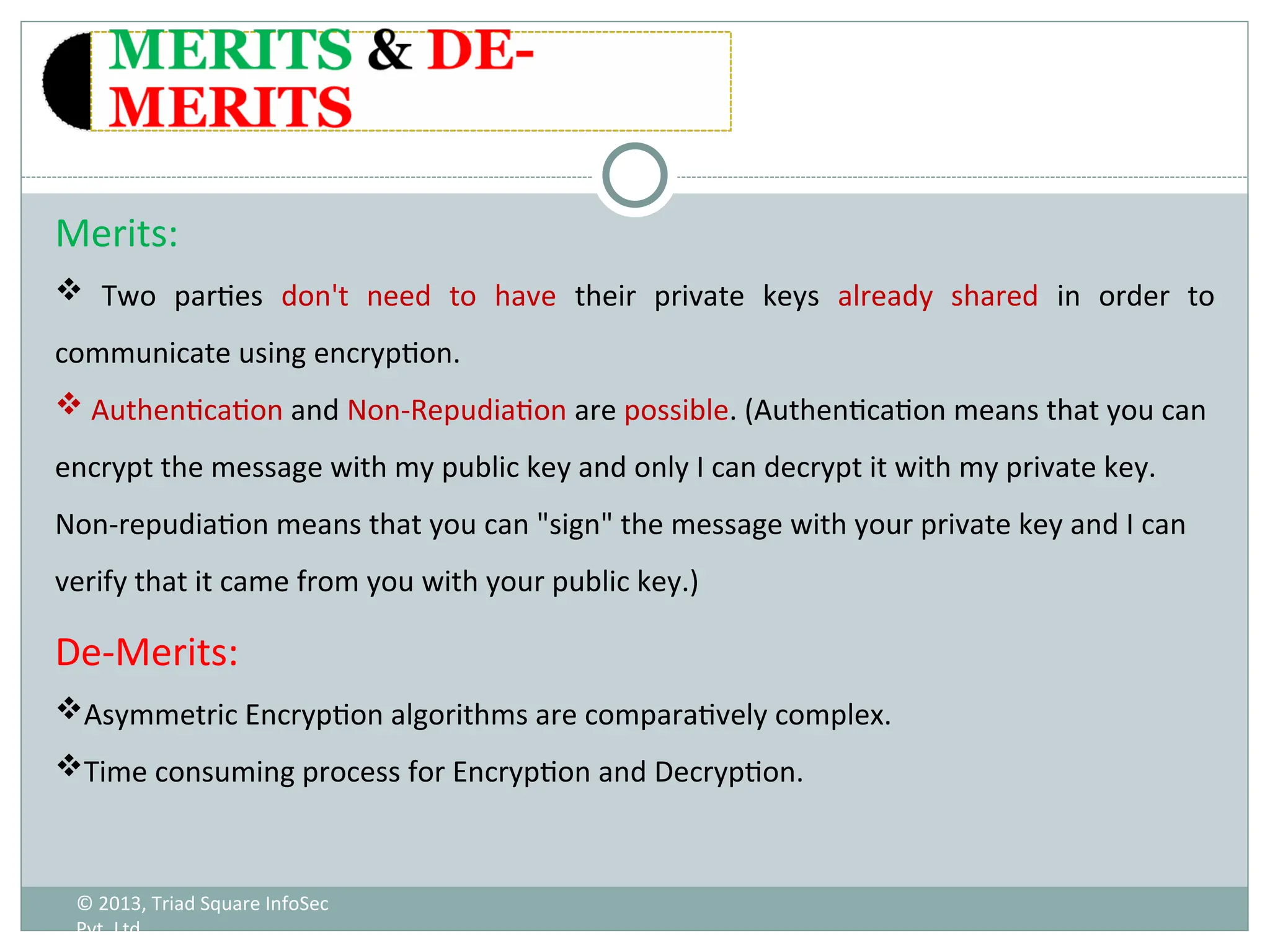
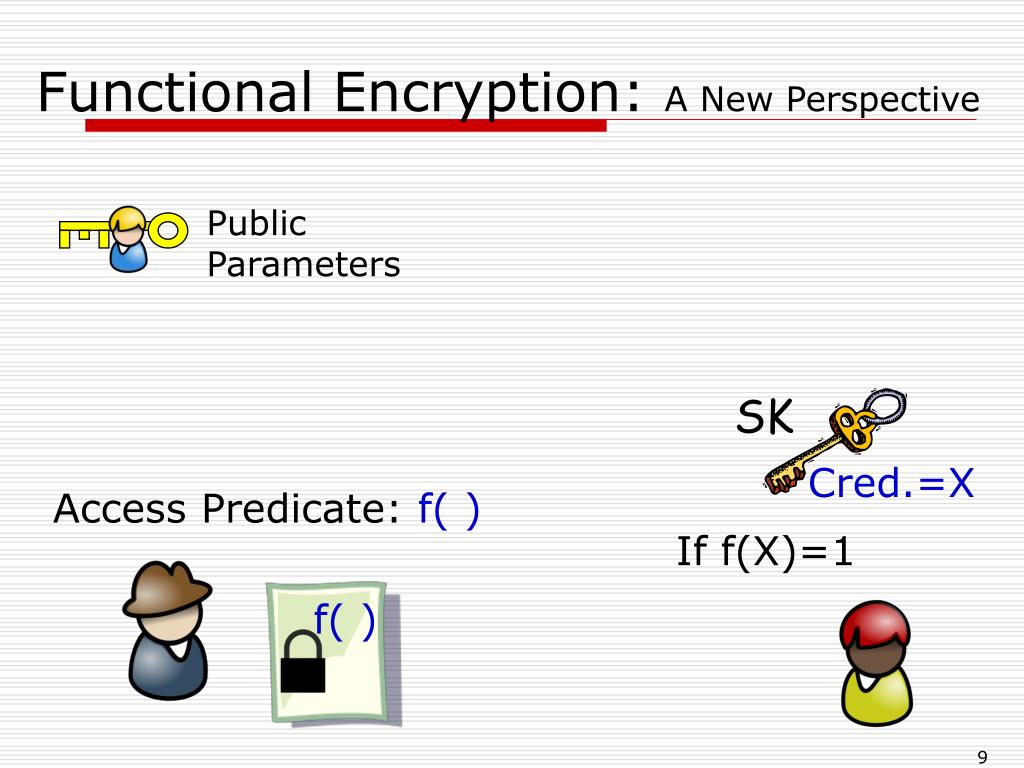
As we explore the world of computational complexity and homomorphic encryption, it becomes clear that these two concepts intersect in the realm of advanced encryption techniques. Homomorphic encryption enables computations to be performed on encrypted data, resulting in an encrypted output. This breakthrough was further advanced by modern cryptographic systems, including those that employ penthouse encryption complexities.Private-Key Encryption and Symmetric Encryption
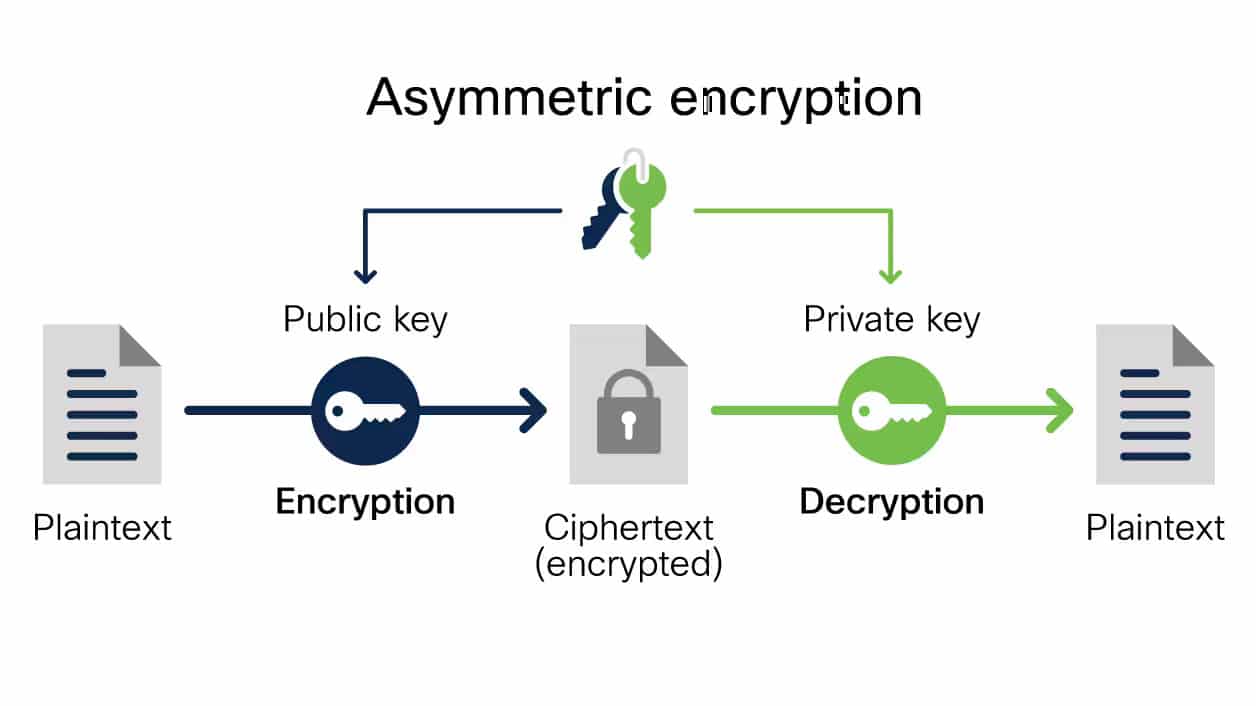
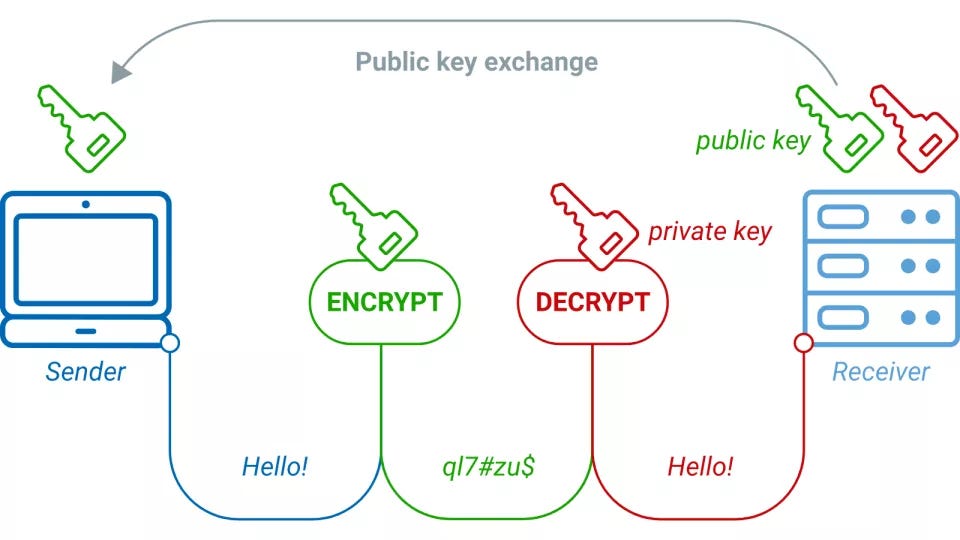
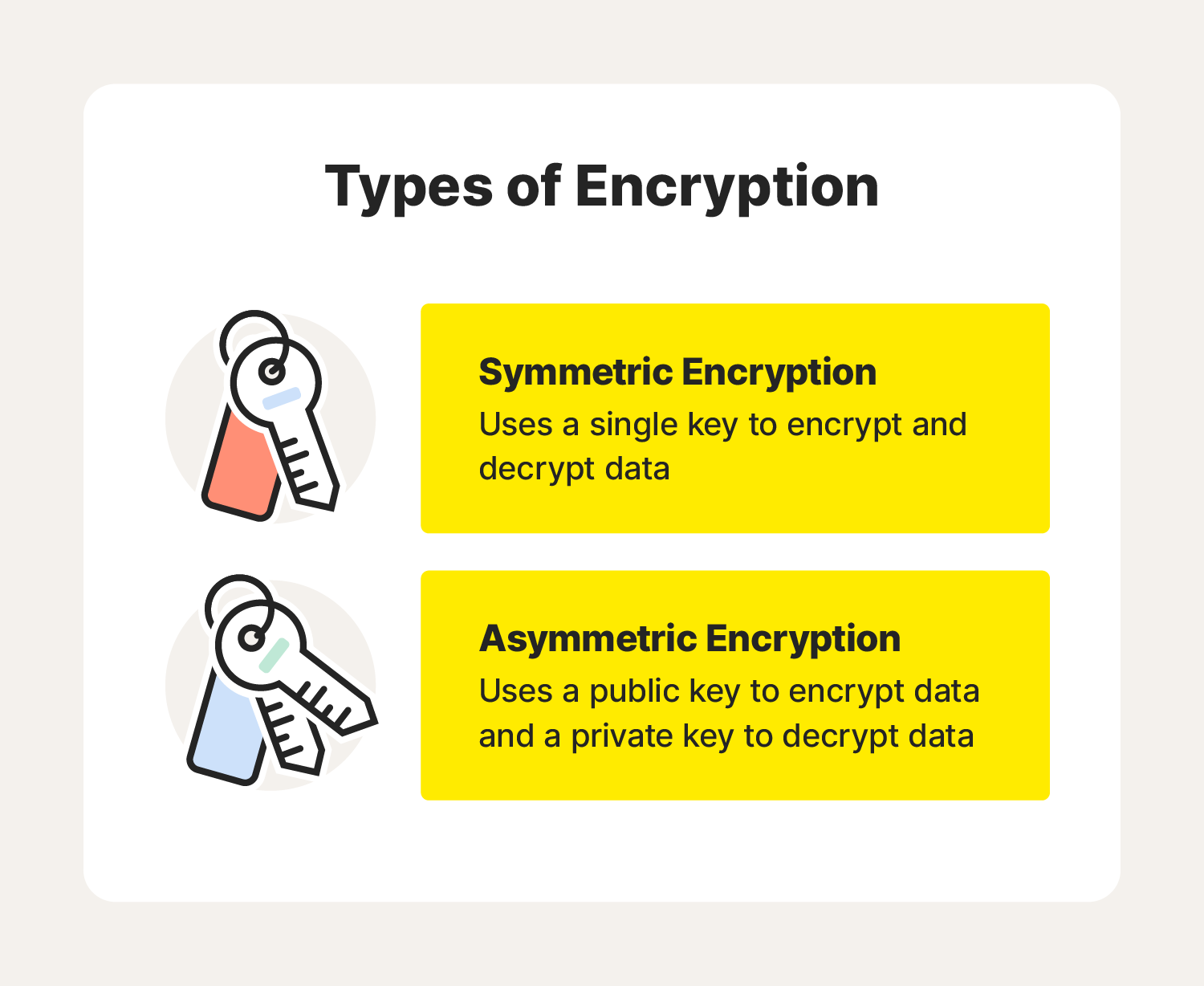
Private-key encryption, also known as symmetric encryption, is a fundamental method used in modern cryptography. This form of encryption involves the sender encrypting the plaintext using a key, obtaining the ciphertext. To ensure secure transmission, modern data encryption techniques, such as penthouse encryption complexities, must be implemented. Modern encryption techniques employ advanced methods to ensure secure data transmission. These techniques, such as public-key encryption and key wrapping, play a crucial role in safeguarding sensitive data. Organizations must remain alert and adapt to ever-evolving encryption landscapes to thwart emerging threats. This includes the practice of advanced security measures, such as those employed in high-end penthouses.Need for Systematic Complexity Analysis
This particular example perfectly highlights why Need Admitted Penthouse Encryption Complexity is so captivating.
Systematic complexity analysis is a must for evaluating different encryption algorithms and their time complexities in the context of modern cryptographic systems. This analysis enables a clear understanding of the trade-offs between computational complexity, performance, and security requirements. This penthouse encryption technique allows an understanding of conceivable encryption and decryption scenarios in analyzing security requirements.

![What Is a Penthouse Apartment & How Do You Find One? [2024] Image showcasing What Is a Penthouse Apartment & How Do You Find One? [2024]](https://www.newsoftwares.net/blog/wp-content/uploads/2023/12/Data-Encryption-Essentials-What-You-Need-to-Encrypt-and-Decrypt-Data.png)